“Cloud penetration testing is a security assessment process in which real-world cyberattacks are simulated against cloud infrastructure, applications, and services to identify vulnerabilities before malicious actors can exploit them.”
Cloud technologies have significantly shifted the conventional methods of deploying applications, storing data, and managing IT infrastructure.
A recent study highlighted a continuous double-digit growth worldwide with spending of over to $500 billion every year due to enterprises migrating to cloud platforms.
While the shift is phenomenal, the challenges introduced alongside narrate a scary story.
- 82% of data breaches involve data stored in the cloud, and misconfiguration remains the leading cause of these incidents.
- Moreover, the average cost of a cloud data breach is estimated to be around $4.45 million, and an average of 277 days to identify and contain such breaches.
This comprehensive guide examines the methodologies, tools, regulatory considerations, and strategic approaches necessary for effective cloud penetration testing in today's threat landscape.
Cloud Penetration Testing: What it is and why is it Necessary

In practice, cloud penetration testing means ethically hacking of one's own cloud environment to discover security weaknesses. Unlike conventional security audits, it does not rely on checklists and configuration reviews.
It involves actively attempting to breach cloud defences. This involves real-time simulation to access S3 buckets, escalate privileges through misconfigured IAM roles, exploit vulnerable APIs, or move laterally across cloud resources.
While the scope of cloud penetration testing is quite clear, the question here is: Why is it even needed?
Well, it is primarily because of two basic reasons:
- The common vulnerabilities and risks in cloud security
- The gaps in traditional penetration testing to identify and mitigate the risks.
To get a clearer understanding, lets break each of these one by one.
Learn more about our Cloud Penetration Testing Engagements.
Common Cloud Vulnerabilities and Security Risks
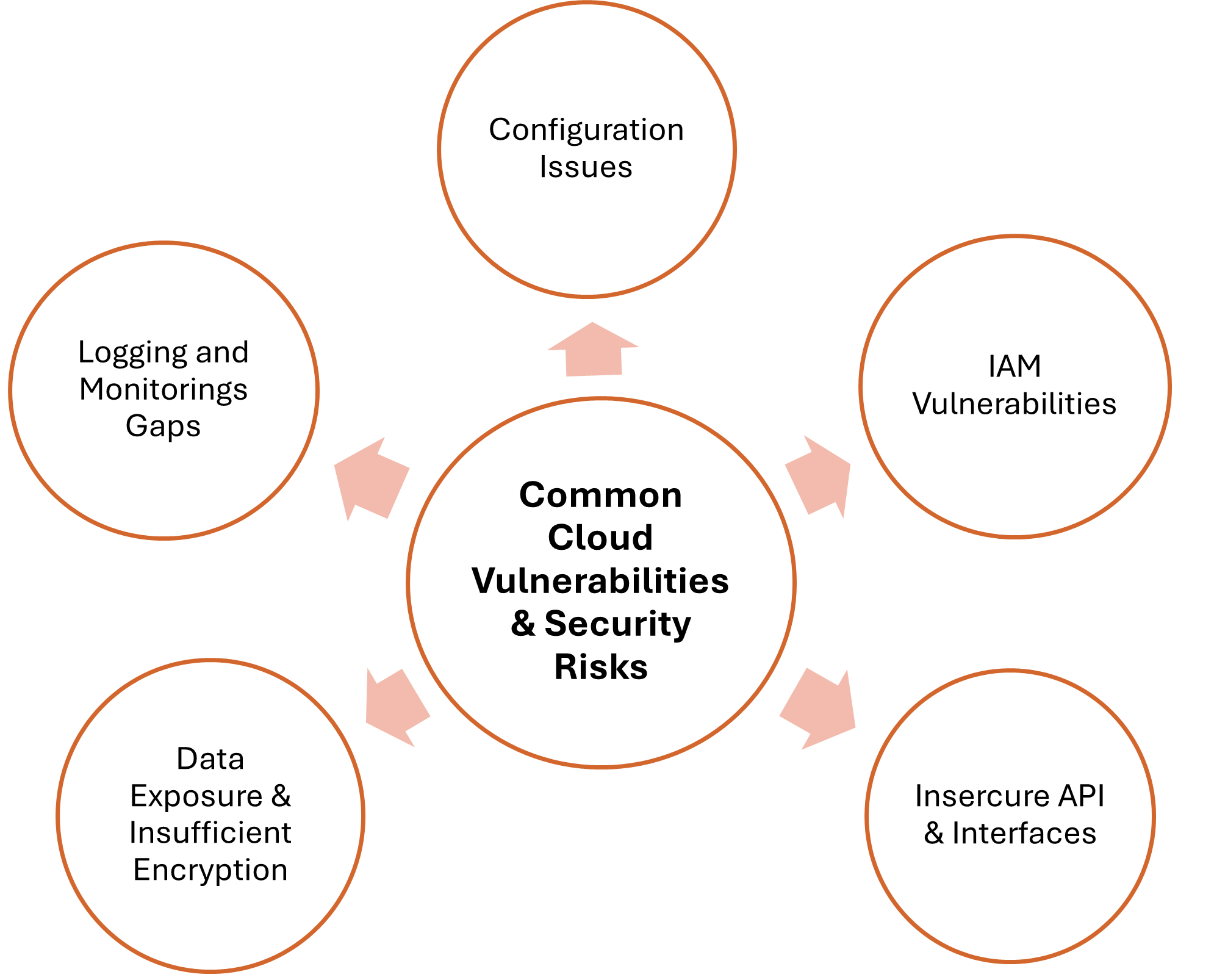
Cloud environments face a unique and evolving threat landscape. Recent data reveals that 80% of organizations experienced at least one cloud security incident in 2024 with businesses facing an average of 1,925 cyberattacks per week. Understanding these threats is essential for effective penetration testing and security posture management.
Misconfigurations
Research shows that 68% of organizations rank misconfiguration as their top cloud security threat, and alarmingly, 82% of these misconfigurations stem from human error rather than software defects.
Some of the most common misconfiguration scenarios include:
- Exposed storage services are frequently misconfigured with public access permissions. Recent findings show that 72% of cloud environments have publicly exposed databases lacking sufficient access controls.
- Many organizations deploy cloud resources with default configurations that prioritize accessibility over security. Default credentials, open network ports, and disabled encryption settings create immediate vulnerabilities.
- Cloud environments are often exposed to virtual machines and serverless instances with sensitive data. Misconfigured security groups, network Access Control Lists (ACLs), and firewall rules often allow unrestricted inbound to the cloud ecosystem from the internet.
Insecure APIs and Interfaces
Application Programming Interfaces (APIs) serve as the backbone of cloud services, but they also represent significant attack surfaces when improperly secured.
Publicly exposed API endpoints, verbose error messages and lack of encryption for API communications create multiple entry points for attackers.
This results in unauthorized access to sensitive data and functionality that can compromise the entire infrastructure.
Identity and Access Management (IAM) Vulnerabilities
IAM misconfigurations enable attackers to gain unauthorized access, escalate privileges, and move laterally across cloud infrastructure. This results into:
- Overprivileged roles and accounts granting excessive permissions to individual users.
- Weak authentication mechanisms with inadequate basic security controls.
- Credential theft and exposure. Research found that 68% cited credential theft and stolen secrets as the fastest-growing cloud infrastructure attack tactics.
- Privilege escalation paths that enable access to exploit permissions to gain higher-level access.
Data Exposure and Insufficient Encryption
Study shows that 54% of data stored in the cloud is classified as sensitive, yet only 8% of respondents encrypt 80% or more of their cloud data. Data stored in databases, object storage, and file systems often lack required encryption that makes it vulnerable to unauthorized access.
Moreover, data moving between cloud services, with a missing or weak Transport Layer Security (TLS) configurations or outdated encryption protocols expose it to foreign interception.
Logging and Monitoring Gaps
Effective security requires visibility into cloud activities. However, 35% of security professionals cite inadequate visibility and control during development as contributors to cloud risks.
Without continuous monitoring, security incidents remain undetected for long time. This gives attackers ample opportunity to exfiltrate data and establish persistence.
In addition, it also leads to critical security events go unrecorded, audit trails lying incomplete, and creates barrier to forensic investigations.
Gaps in Traditional Penetration Testing
While the broad landscape of threats and vulnerabilities already justifies the need for a secure mechanism that extend beyond automated scanners. Moreover, its burning needs are also a result of gaps in traditional pentesting methodologies.
Traditional penetration testing was designed for predictable, static environments with clear boundaries and perimeters. Security teams could map every asset, control every configuration, and define explicit network perimeters.
On the other hand, cloud penetration testing demands a fundamentally different approach. The dynamic nature of cloud infrastructure includes publicly exposed storage buckets and overly permissive identity policies to insecure APIs, and complex containerized architectures.
Moreover, the shared responsibility model, and the complexity of Identity Access Management (IAM) policies create unique security challenges that traditional methods simply cannot address.
Traditional Penetration Testing vs Cloud Penetration Testing
| Aspect | Traditional Penetration Testing | Cloud Penetration Testing |
|---|---|---|
| Infrastructure | Fixed, on premises with physical boundaries | Dynamic, multi-region distributed infrastructure |
| Network Perimeter | Defined perimeter with firewalls | Fluid perimeter with API endpoints and internet-facing services |
| Access Control | Network-based (VLANs, firewalls) | IAM policies, RBAC, API keys |
| Authorization | Organization approval only | Organization + CSP approval required |
| Attack Surface | Servers, workstations, network devices | Storage buckets, serverless, containers, APIs, microservices |
| Configuration | Manual hardware/software setup | IaC, automated deployments, drift risks |
| Responsibility | Organization owns all security layers | Shared: Provider (infrastructure), Customer (data, apps, configs) |
| Data Storage | Centralized on-premises databases | Distributed (S3, Blob Storage, RDS, data lakes) |
How Cloud Penetration Testing Works?
Cloud penetration testing operates through a systematic approach that mirrors how real attackers target cloud environments, but with proper authorization and documentation. The methodology adapts to the dynamic, distributed nature of cloud infrastructure while maintaining rigor and thoroughness.
| Phase | Description |
|---|---|
| Authorization & Scope Definition | The process begins with obtaining the necessary data access and permissions from cloud service providers. Unauthorized testing at this stage can trigger security alerts, violate terms of service, or result in account suspension. In parallel, teams define the scope by identifying which cloud resources, regions, and services are included, while establishing clear boundaries for testing activities. |
| Intelligence Gathering | Security experts map the cloud environment’s architecture by identifying exposed services, documenting API endpoints, analysing IAM structures, and understanding data flows between cloud components. Unlike traditional networks with static topologies, cloud environments require continuous reconnaissance due to dynamic scaling. |
| Attack Simulation & Exploitation | Testers simulate real-world attack scenarios by attempting to exploit misconfigurations in storage services, escalate privileges through IAM weaknesses, bypass authentication controls, and probe APIs for vulnerabilities. Successful exploits are documented with detailed reproduction steps, while failed attempts help validate effective security controls. |
| Post-Exploitation Analysis | This phase assesses what an attacker could achieve after initial compromise. Testers analyse potential lateral movement paths, identify sensitive data exposure risks, and evaluate the effectiveness of monitoring and detection mechanisms, revealing the true business impact of discovered vulnerabilities. |
| Reporting & Remediation Guidance | A comprehensive report is delivered with prioritized findings based on business risk. This includes actionable remediation recommendations aligned with cloud security best practices, along with evidence supporting each identified vulnerability. |
Types of Cloud Penetration Testing
While the process of cloud penetration testing encompasses multiple specialized approaches, there are different types that address different security dimensions.
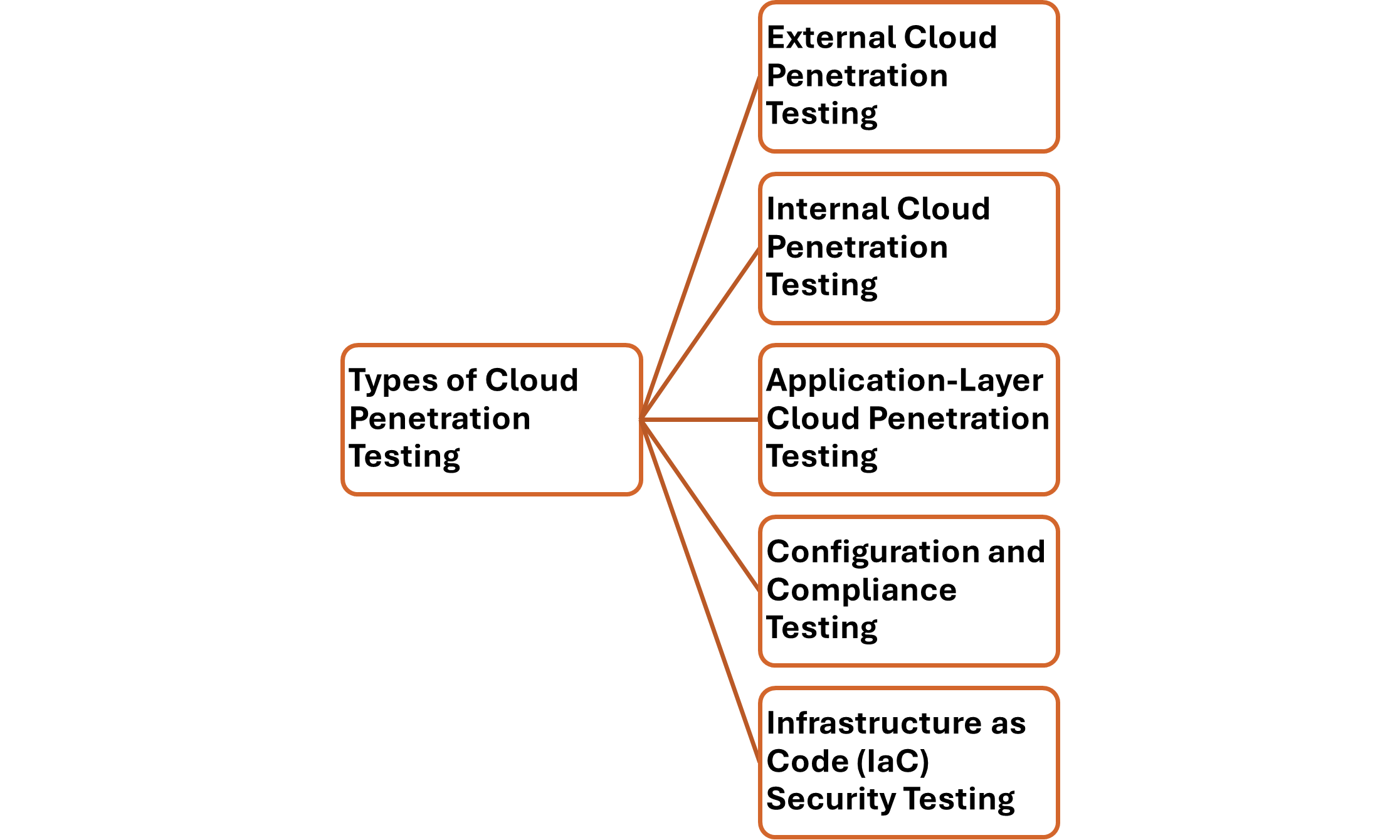
External Cloud Penetration Testing
External testing examines your cloud infrastructure from an outside attacker's perspective. It focuses on internet-facing assets and publicly accessible resources.
Testers target exposed APIs, public storage buckets, web applications hosted in the cloud, and any services accessible without authentication.
Internal Cloud Penetration Testing
Internal testing assumes an attacker has already gained some level of access to your cloud environment. It assumes that the privilege escalated as a result of through compromised credentials, social engineering, or other means.
This type focuses on what damage an insider threat or compromised account could inflict. Testers work with limited initial access to explore escalation opportunities, lateral movement, access to data repositories, and exploitation of trust relationships.
Application-Layer Cloud Penetration Testing
This specialized testing targets applications deployed in cloud environments. It examines how cloud-specific features and configurations affect application security.
Unlike generic application testing, cloud application testing considers serverless architectures, containerized deployments, cloud-native authentication, and API gateway configurations.
Configuration and Compliance Testing
Configuration testing systematically reviews cloud infrastructure against security benchmarks, compliance frameworks, and industry practices. This approach combines automated scanning with manual verification to identify misconfigurations that automated tools might miss.
The process examines IAM policies for:
- overly permissive access,
- storage services for public exposure,
- network configurations,
- encryption settings and in transit, and
- logging configurations for adequate audit trails
Infrastructure as Code (IaC) Security Testing
IaC testing examines the security of automated deployment templates and scripts before they provision cloud resources. This approach prevents vulnerabilities from being deployed.
Testers analyse Terraform configurations, CloudFormation templates, and Kubernetes manifests for security weaknesses. Additionally, they check how automation scripts handle data and credentials and validate security controls defined in code.
Platform-Specific Cloud Penetration Testing & Their Requirements
Alongside, the overall methodology used for pentesting cloud systems, each major cloud platform presents distinct architectures, service models, and testing requirements that demand specialized expertise.
| Platform | Primary Security Model Focus | Key Testing Areas | Testing Permissions / Restrictions | Critical Architectural Consideration |
|---|---|---|---|---|
| Amazon Web Services (AWS) | Service-centric security with policy-driven access control |
|
Most penetration testing allowed without approval. Additionally, advance notification is required for DDoS simulation, port flooding, and protocol flooding. | Shared Responsibility Model, AWS secures infrastructure; customer secures configurations, workloads, and data. |
| Microsoft Azure | Identity-centric security driven by centralized access governance |
|
Penetration testing generally permitted without prior notification, provided other tenants/services are not impacted. | RBAC hierarchy cascading across Management Groups |
| Google Cloud Platform (GCP) | Resource-hierarchy-based identity and policy management |
|
Testing allowed without pre-approval within owned projects and compliant with platform ToS. | Hierarchical IAM interaction across Organization |
End Notes
As organizations continue migrating critical systems and sensitive workloads to cloud, the need for rigorous, recurring testing increases. Cloud environments expand and change rapidly, exposing new services, identities, and attack paths.
Effective cloud security depends on understanding how operate. A well executed pentest provides that visibility and ensures maintenance of a secure cloud posture.



