Advancing into future, the industrial revolution Industry 4.0 has already taken its momentum At the pinnacle of this movement are the Operational Technologies (OT), the machines running behind every industrial facility.
However, as these OT systems evolve so does increases the threats to its security.
“On February 5, 2021, a water plant operator in Oldsmar, Florida noticed his mouse moving on its own across the screen. This wasn’t just another system access by the IT team; it was a sophisticated cyberattack on the plant’s operational system. Someone had remotely accessed the water plant and intended to increase sodium hydroxide levels to poison the water supply.”
Incidents like this exemplifies the growing threat landscape in connected industrial environment. Nevertheless, this is the new reality, the Programmable Logic Controllers (PLCs) controlling production line isn’t isolated anymore, it’s networked, accessible, and vulnerable. The same connectivity that enables remote monitoring and predictive maintenance also creates pathways for cyber threats.
Moreover, this is not just about PLC’s as industrial facilities advance with integration of IT and OT networks for efficiency gains, they are also inheriting new vulnerabilities.
To effectively mitigate the complexities, NIST framework introduces stringent guidelines for organizations managing critical infrastructure. This article explores what OT security means for industrial operations, how it differs from traditional IT security and its challenges and benefits.
What is Operation Technology (OT)?
In simple terms, Operational Technology (OT) refers to technology and machines running behind industrial plants (i.e. power plants, smart manufacturing factories etc.) to keep them up and running. It encompasses all the hardware and software systems that monitors, detects, and control physical devices, processes, and infrastructure in industrial environments namely:
- Supervisory Control & Data Acquisition (SCADA)
- Industrial Control Systems (ICS)
- Programmable Logic Controllers (PLCs)
| Industrial Control Systems (ICS) | Supervisory Control & Data Acquisition (SCADA) | Programmable Logic Controllers (PLCs) |
| Industrial Control Systems (ICS) serve as the overarching framework that manages and controls industrial processes. These systems integrate various hardware and software components to automate production lines, regulate equipment performance, ensure operational efficiency, and trigger safety shutdowns when parameters exceed safe thresholds. | SCADA systems provide centralized monitoring and control capabilities for geographically distributed assets and processes spanning across vast areas. They collect data from remote locations, transmit information to central a control room, and enable operators to visualize system-wide performance and issue control commands from a single operations centre. | Programmable Logic Controllers are ruggedized industrial computers designed to execute control logic in harsh environments, directly interfacing with sensors, actuators, motors, and valves to control specific equipment or processes. These devices continuously scan inputs, execute programmed logic in real-time, and activate outputs that control physical equipment with the reliability high pressure conditions. |
Security Challenges in Operation Technology (OT) Management
Industrial infrastructures are the backbone of every economy today. However, in the race to be a leader, its security management is often found to be a weak link that becomes attacker’s prime target. The primary causes of these challenges are often quite common highlighted during various discussions:

- Legacy Systems and Extended Lifecycles
- System Availability
- Technological Complexity
- Visibility and Asset Management Gaps
- Vendor Dependencies and Supply Chain Risks
While technology has significantly developed over years, the most pervasive challenge in OT security stems from the prevalence of legacy systems.
This challenge is often misunderstood, the real issue isn’t age, it’s that these systems were designed when physical isolation was the security model. A 1995 PLC assumed requiring physical access to reprogram, the same PLC sits on a network where a compromised laptop three hops away can reach it. We’re not dealing with ‘old’ systems; we’re dealing with systems operating in a threat environment they were never designed for.
OT environments demand near 100% uptime, making traditional security practices like regular patching, rebooting, and system updates extremely challenging.
A manufacturing facility operating 24/7 cannot afford unexpected downtime for security patches. This availability requirement means that security measures must be carefully planned around narrow maintenance windows, often measured in hours per year. As a result, known vulnerabilities may remain unpatched for extended periods, creating persistent security gaps that attackers can exploit.
The increasing convergence of IT and OT networks driven by Industry 4.0 initiatives, has dismantled the traditional air-gap isolation that once protected industrial systems. While this connectivity enables operational efficiencies and predictive maintenance, it also creates pathways for cyber threats to migrate from corporate networks into operational environments.
Managing security across this converged landscape requires understanding both domains, yet many organizations lack cross-functional expertise in both.
Many organizations lack complete visibility into their OT environments.
Unlike IT networks with centralized asset management systems, OT networks often contain undocumented devices, shadow connections, and legacy equipment with unknown configurations. This lack of comprehensive asset inventory makes it impossible to assess risk accurately, implement appropriate security controls, or detect anomalous behaviour. Organizations cannot protect what they cannot see, yet achieving complete OT network visibility without disrupting operations remains a significant challenge.
OT environments typically rely on specialized equipment from specific vendors, creating dependency relationships that complicate security efforts. Proprietary systems may lock organizations into vendor-specific security solutions or timelines for patches and updates.
Additionally, the OT supply chain introduces multiple third-party access points that can become attack vectors. Managing these vendor relationships while maintaining security requires rigorous third-party risk management programs that many organizations are still developing.
What is OT Security?
Operation Technology or OT security is a comprehensive approach combining people, processes, and technology to defend against cyber critical challenges of industrial environments.
It is focused on securing the hardware, software, and network systems that monitor and control physical industrial processes. Unlike traditional cybersecurity that safeguards data and information systems, OT security ensures the confidentiality and continuous availability of industrial control systems (ICS), SCADA networks, programmable logic controllers (PLCs), and distributed control systems (DCS) that power essential services.
This overall security architecture follows a multi-layered approach with components that addresses the unique challenges to secure existing setups or designing a new one.
- OT Security Architecture for Management of Existing Setups
- OT Security Architecture for Establishing a New Setup
For organizations managing existing OT infrastructure, the following architecture illustrates the layered security model commonly applied to protect operational environments. The focus here is on compensating controls, network segmentation, access management, and anomaly detection that can be retrofitted without requiring a complete system overhaul.
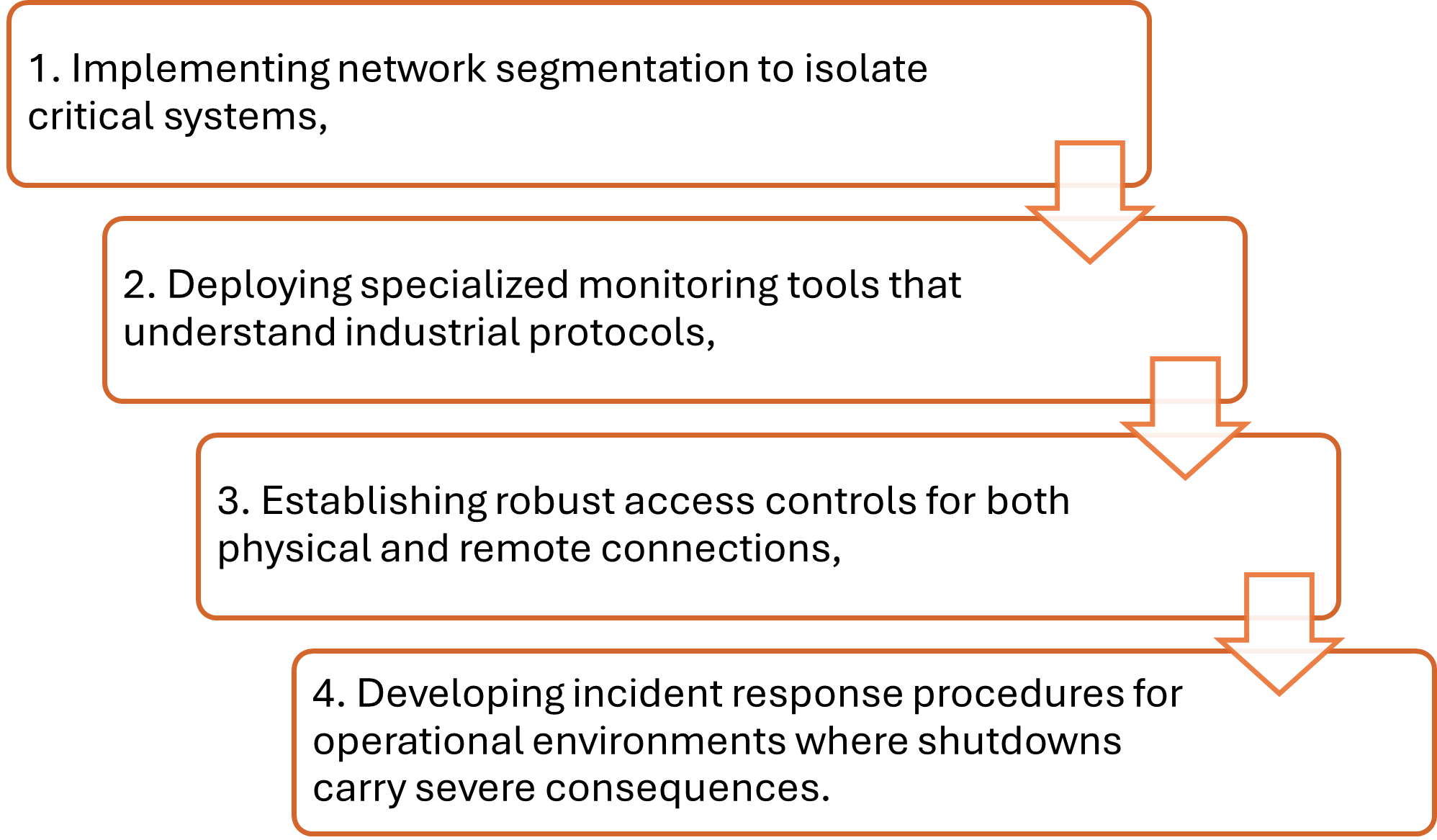
When designing a new OT network from the ground up, organizations can embed security by design. Two capabilities deserve particular emphasis in greenfield deployments.
First, structured patch management, this refers that new architectures should include a dedicated patch testing environment that mirrors production, It should enable security updates to be validated and applied during planned maintenance windows without risking operational disruption.
Second, continuous monitoring, which means new deployments should incorporate purpose-built OT monitoring solutions (such as Claroty, Nozomi Networks, or Dragos) that provide passive, agentless visibility into industrial protocol traffic, enabling early detection of anomalous behaviour.
Difference Between OT Security and IT Security

While IT and OT security both aim to protect against cyber threats, they differ fundamentally in priorities, constraints, and methodologies due to the distinct nature of their environments.
- The primary difference between OT and IT security lies in its structure. IT security follows the traditional CIA triad, Confidentiality, Integrity, Availability in a sequence, where confidentiality of data comes first. Systems can be temporarily taken offline if needed.
However, OT security reverses this entirely prioritizing Availability as industrial processes cannot stop meanwhile integrity ensures accurate control and sensor data. Nevertheless, it is worth noting that in OT environments, particularly manufacturing, Integrity and Availability are closely intertwined. A compromised system that continues operating but produces incorrect outputs (e.g., flawed parts on a production line or manipulated sensor readings) may be as damaging as one that stops entirely. However, in power supply or process industries, a full shutdown may be preferable to operating with corrupted control data. Confidentiality ranks last since operational continuity trumps data privacy.
- IT and OT security also differ in operational constraints. While IT systems tolerate some latency and can undergo regular updates with minimal disruption. OT systems operate in real-time with millisecond-level timing requirements where even slight delays can cause safety incidents or equipment damage. Patching requires extensive testing and rare maintenance windows, often leaving systems unpatched for extended periods.
- Furthermore, the tools and technologies used across the OT and IT differs widely. OT security requires specialized solutions that understand industrial protocols like Modbus and DNP3, provide passive monitoring capabilities, and respect real-time operational constraints.
Why Compliance with OT Standards Doesn’t Equal Security?
Compliance frameworks give you a checklist. Security requires judgment.
A facility can technically comply with NIST’s “implement network segmentation” by installing a firewall between IT and OT networks. Checking the boxes, enables you passing the audit. But if that firewall allows 47 different protocols because “operations needs access,” the system isn’t actually secured.
The real problem runs deeper. Most OT standards were written to address every industry and every scenario; they’re necessarily generic, they tell you to perform risk assessments and implement “defence in depth.”
However, it doesn’t tell you that risk in a pharmaceutical plant differs completely from a steel mill. They can’t account for the maintenance contractor connecting an infected laptop directly to your SCADA network, or the production manager bypassing controls because they add three seconds to a repeated process.
This is where the role of OT security testing comes in.
OT security testing moves beyond checkbox compliance to validate your defences against real threats. It involves simulating a real time attack over your systems assessing the difference between having a documented incident response plan and running a tabletop exercise.
Benefits of OT Security Testing
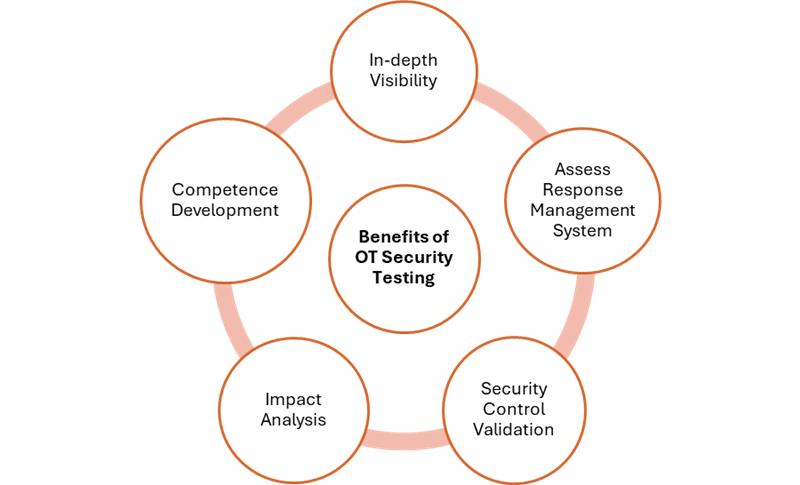
The implementation of a robust OT security testing not only help mitigate the challenge of security but also delivers significant advantages that extend beyond basic threat protection.
- Provides In-depth Visibility
- Strength Assessment of Response Management Systems
- Validating Security Controls
- Impact Analysis
- Developing Competence
Every OT assessment uncovers assets the organization didn’t know were on their network. Not just a few its often about 15-30% of devices being completely undocumented. This includes wireless access points a contractor installed years ago for “temporary” remote access.
You can’t protect what you can’t see. Testing forces complete network visibility, revealing the actual attack surface rather than the theoretical one in your network diagrams.
Incident response plans look great in PowerPoint. But when a simulated ransomware attack hits, security teams often find the actual loopholes in the plan. Testing creates controlled failure, the one you can learn from without actual production losses.
Often when security controls are validated in industrial setting it’s often noted that there is a significant gap between documented policies and real-world implementation
Documentation may state that application whitelisting is enabled on all Human Machine Interfaces (HMIs), yet testing can reveal a different scenario with certain blocked components. Testing of OT systems offers transparency to validate operational deployments against technical documentations.
Risk assessments assign scores: “high,” “medium,” “low.” Testing shows you what happens when that “medium” risk vulnerability in your SCADA system gets exploited. Can an attacker move laterally to the safety instrumented system? Can they modify setpoints without triggering alarms? How long before your team would even notice unauthorized access?
Facility operators may understand production inside and out. Nevertheless, most of them know nothing about cyber threats. Testing, especially red team exercises, trains them to recognize anomalous behaviour.
Security awareness training with generic phishing examples doesn’t resonate in industrial environments. When teams experience a simulated attack targeting your actual systems, using your actual protocols, the lessons stick.
Wrapping Up
The journey toward robust OT security is not a destination but a continuous learning process. As industrial infrastructure becomes increasingly interconnected and adversaries grow more sophisticated, organizations must shift from reactive defence to proactive resilience.
This requires fostering a security-first culture where operational teams and cybersecurity professionals collaborate seamlessly, breaking down traditional silos between IT and OT domains. Moreover, investment in OT security testing, leveraging threat detectors, zero-trust architectures, and continuous monitoring tools gives the edge in this fast-paced environment.


