In the last few decades, the digital infrastructure landscape has evolved drastically and at the core of this change are embedded systems. These micro-devices act as specialized computing chips that combines hardware and software capabilities to perform dedicated tasks.
As transformational as it sounds, these systems are equally vulnerable. Embedded devices blur the physical and digital boundary in the infrastructure and technologies used, exposing the surface area of attacks. Moreover, as these systems are interconnected, the impact of a single breach can cascade across millions of deployed units.
To ensure effective mitigation and prevent occurrence of any such attacks, embedded penetration testing stands out as an efficient solution. This article will explore the comprehensive methodologies for embedded penetration testing and address the unique challenges that emerge across the process.
Why is Embedded Penetration Testing Necessary?
The necessity for embedded penetration testing stems from the inherent vulnerabilities plaguing modern embedded systems and IoT devices. According to recent security analysis, 98% of IoT traffic lacks encryption, while 57% of devices contain medium to high-severity vulnerabilities.
Moreover, as organizations continue their digital transformation, the security gap continues to widen with:
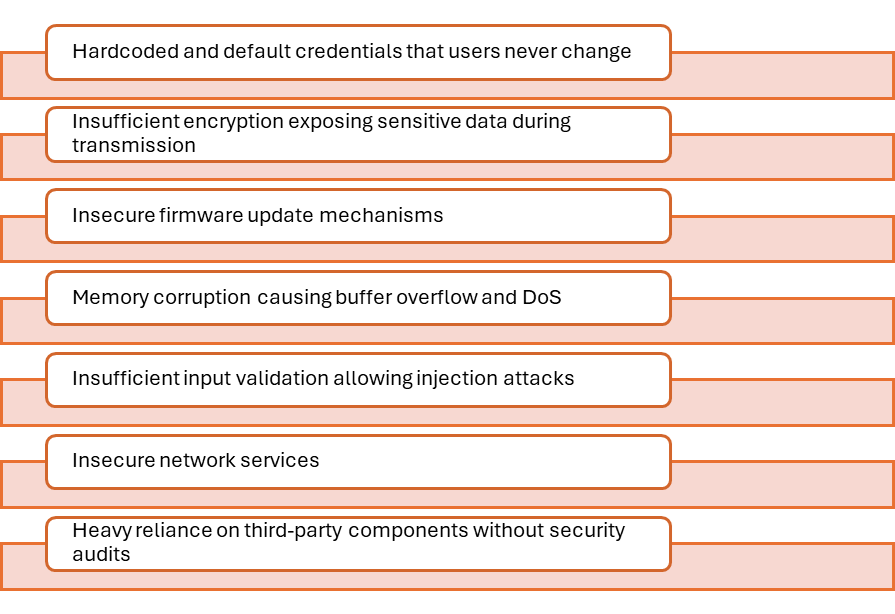
Traditional reactive approaches are inadequate to fix these issues. They still wait for breaches to occur before implementing fixes. This disconnects between threat reality and security preparedness makes embedded penetration testing essential for any organization deploying these systems at scale.
Learn more about our Embedded Penetration Testing Engagements.
How Embedded Penetration Testing Works?
Embedded penetration testing follows a structured, multi-phase approach that systematically examines every layer of an embedded system.
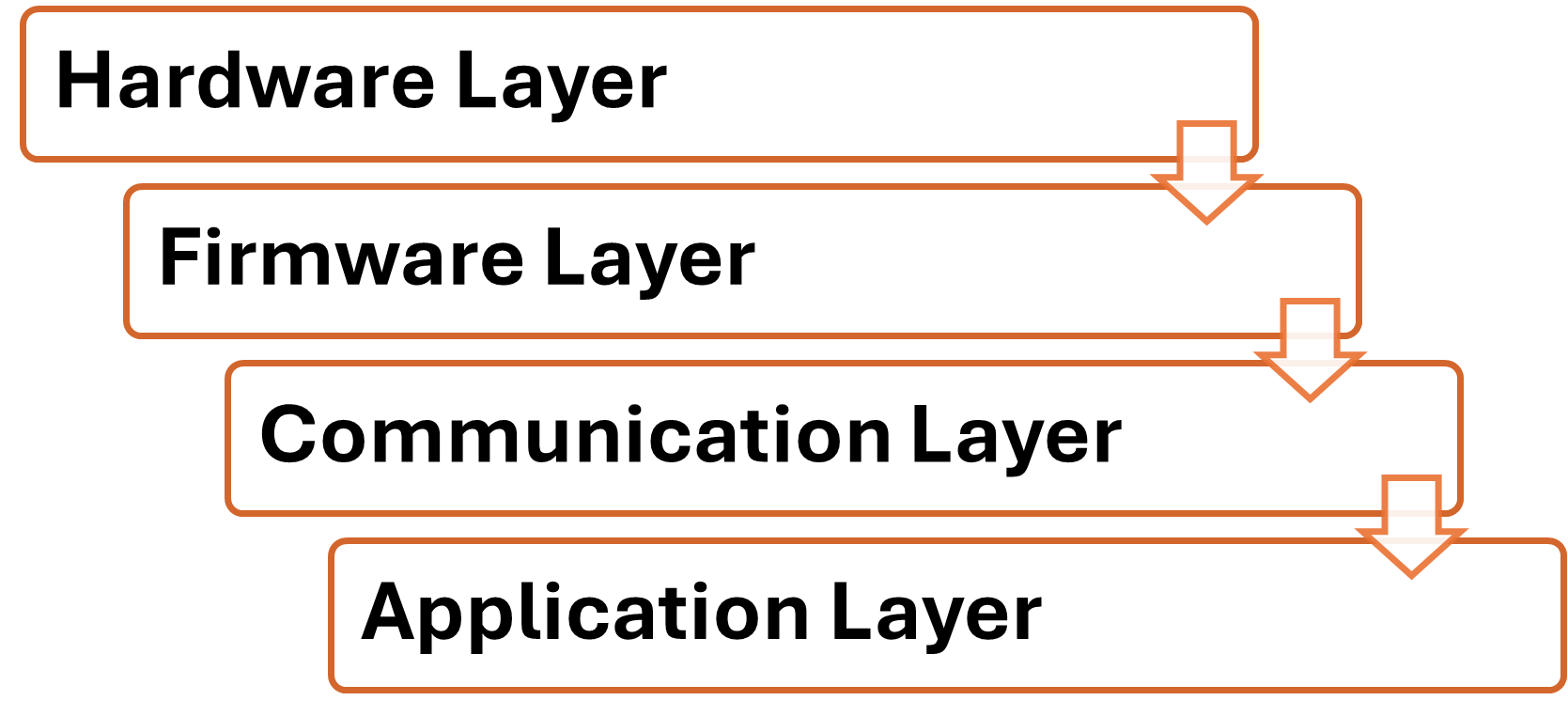
Unlike traditional penetration testing that focuses primarily on software applications, embedded testing requires a hybrid methodology that bridges hardware analysis, firmware reverse engineering, and protocol security assessment.
The whole process is further divided into various stages:
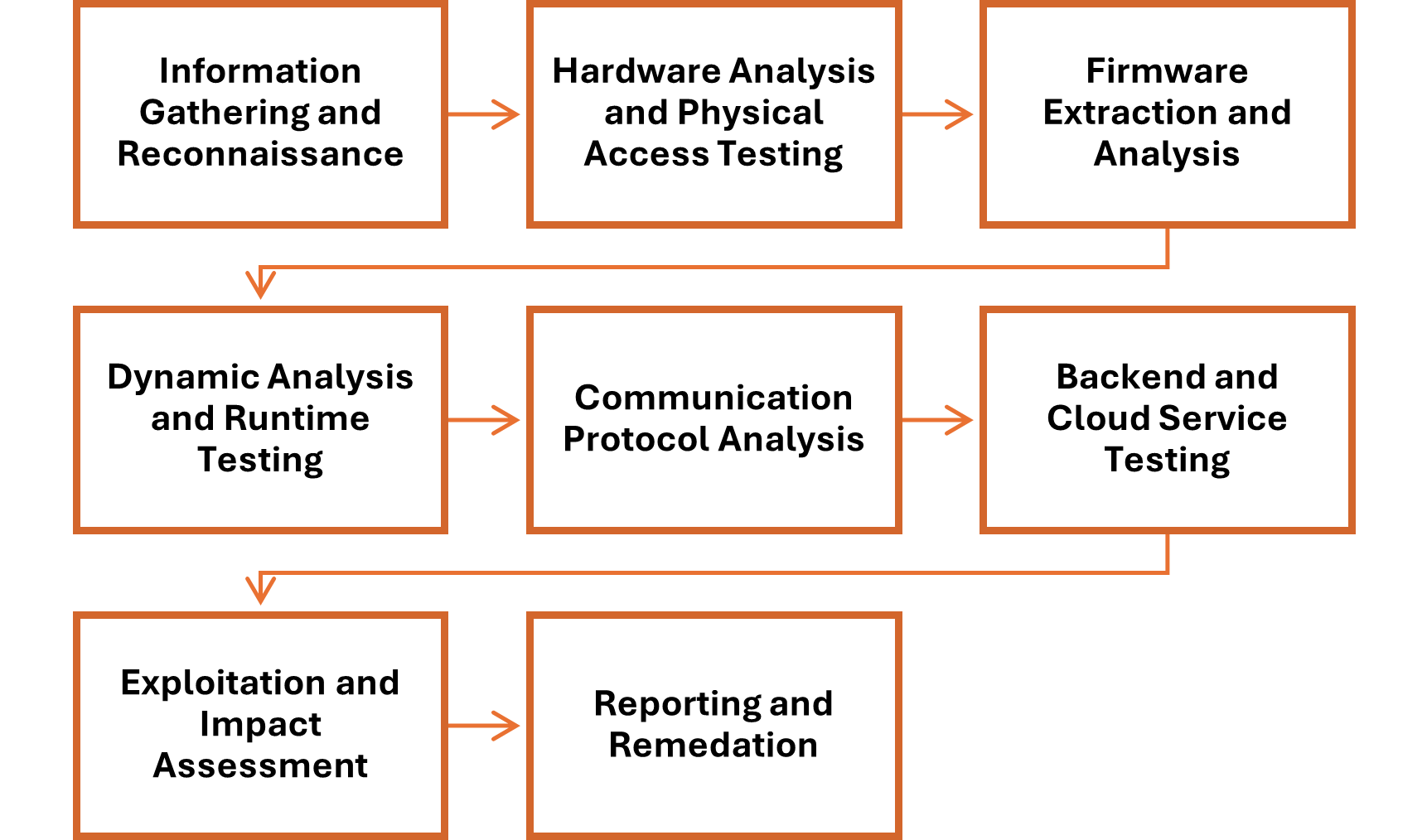
Phase 1: Information Gathering and Reconnaissance
The testing process begins with intelligence gathering about the target device. It begins with collection of technical documentation, identifying the device architecture, mapping communication interfaces, and cataloguing all external connections.
Engineers also perform passive reconnaissance by monitoring network traffic, identifying communication protocols, and documenting the device’s behaviour under normal operating conditions.
Phase 2: Hardware Analysis and Physical Access Testing
Once all the information about devices is gathered the next step involves hardware analysis and physical security assessment. This examines the device’s resistance to tampering and unauthorized access.
The process combines the examination of circuit board layout to identify debug interfaces such as JTAG and UART ports, locate memory chips, and search for test points that might provide unauthorized access to system internals. This phase often involves opening the device enclosure to expose the PCB, identification of components, and using mustimeters and logic analysers to trace connections between chips and identify serial communication protocols.
Engineers further attempt to extract firmware from flash memory chips using JTAG/SWD debuggers, which connect to standard debug interfaces. For direct memory access, flash memory programmers read chips of SMD type in‑circuit, or otherwise after desoldering them using hot air rework stations and microscopes.
Phase 3: Firmware Extraction and Analysis
Firmware represents the core software controlling embedded devices, making it a critical target for attackers. In simple words, the process involves obtaining and examining the software that controls hardware devices.
The extraction methods vary depending on device architecture and available access points. The process extracts firmware through debug interfaces, directly from memory chips using chip-off techniques, by intercepting over-the-air updates, or through bootloader vulnerabilities.
Once extracted, the firmware undergoes static analysis that varies by firmware type. For file system‑based firmware, analysis identifies file signatures, extracts embedded file systems, and detects compression or encryption schemes. On the other hand, for RTOS‑based systems, which lack a conventional file system, engineers analyse the binary image directly, examining memory layouts, task structures, and interrupt handlers. This distinction is critical, as RTOS firmware requires dedicated reverse engineering, tooling and methodology.
Phase 4: Dynamic Analysis and Runtime Testing
Dynamic analysis involves executing the firmware in controlled environments to observe its runtime behaviour. This involves creating emulated environments using processor emulation software or actual hardware testbeds, monitor system calls and memory access patterns, and perform fuzzing to trigger unexpected behaviours.
Debuggers attached to running systems provide real-time visibility into code execution paths and memory states. Coverage-guided fuzzing tools automatically discover memory corruption vulnerabilities by generating intelligent test inputs. This phase uncovers vulnerabilities that only manifest during execution, such as buffer overflows, race conditions, improper error handling, and authentication bypass opportunities.
Phase 5: Communication Protocol Analysis
Embedded devices communicate through various protocols including CAN, Ethernet, NFC, Wi-Fi, Bluetooth, Zigbee, LoRa, and proprietary RF protocols. The communication protocol analysis basically intercepts and analyses these communications to identify encryption weaknesses, authentication flaws, replay attack vulnerabilities, and insecure data transmission practices.
It involves capturing traffic between devices using packet analysers for:
- IP-based networks,
- wireless sniffers for Bluetooth and RF communications, and
- software-defined radios for analysing custom wireless protocols.
The process further follows decoding proprietary protocols, identify command structures, and test for man-in-the-middle attack susceptibility.
Phase 6: Backend and Cloud Service Testing
Modern embedded devices are increasingly integrated with cloud‑based backend infrastructure and REST or MQTT APIs. Engineers assess these backend services following established standards such as the OWASP Web Security Testing Guide and the OWASP Top 10, examining API authentication mechanisms, testing for injection vulnerabilities, analysing data storage security, and validating certificate implementations.
Web application testing proxies intercept and modify traffic between devices and cloud This ensures that a compromised backend cannot be exploited to attack other devices sharing the same infrastructure.
Phase 7: Exploitation and Impact Assessment
After vulnerabilities are identified across different layers of embedded systems, testers attempt to chain multiple weaknesses together to demonstrate realistic attack scenarios. Moreover, custom scripts and purpose-built tools are used instead of generic exploitation frameworks, to assess the actual risk posed by discovered issues rather than relying on theoretical severity ratings.
Successful exploitation demonstrates how attackers could gain unauthorized access, extract sensitive data, modify device behaviour, or create persistent backdoors. Impact assessment quantifies the business and operational consequences, helping organizations prioritize remediation efforts based on actual risk.
Phase 8: Reporting and Remediation
The final phase of the embedded pentesting focuses on delivering comprehensive documentation of:
- discovered vulnerabilities,
- proof-of-concept exploits,
- risk ratings based on CVSS Base Score 3.1, and
- detailed remediation recommendations.
These reports provide both executive summaries for management and technical details for development teams implementing fixes, ensuring that vulnerabilities are properly understood and addressed across organizational levels.
Challenges and Best Practices for Embedded Pentesting at Scale
While embedded penetration testing provides critical security insights, conducting these assessments at scale introduces significant operational, technical, and logistical challenges.
Industries such as manufacturing, automotive, and healthcare rely on fleets of thousands or millions of embedded devices, each presenting unique testing obstacles that demand strategic approaches and tailored methodologies
Device Diversity and Fragmentation
Resource and Time Constraints
Logistic Challenges
Documentation and Proprietary Systems
Firmware Complexity
The embedded ecosystem encompasses vast device diversity. Organizations deploy products across different combination of chips from different vendors that includes CPUs, network controllers, Wi‑Fi and Bluetooth modules, and flash memory, each bringing its own firmware, driver stack, and software supply chain, operating systems, and communication protocols.
Additionally, each device family requires specialized testing tools and architecture-specific expertise, preventing direct replication of testing methodologies across product lines.
Comprehensive embedded penetration testing is inherently time intensive. While initial analysis of a device may take a day or less, invasive testing methods such as fault injection and side‑channel analysis can extend the timelines. When organizations need to assess dozens of device models across product portfolios, the cumulative time investment becomes prohibitive.
Budget limitations compound this challenge. Embedded testing requires expensive specialized equipment, trained security researchers with niche skill sets, and dedicated laboratory environments. Small to mid-sized organizations often lack the capital to invest in comprehensive testing infrastructure, forcing them to prioritize which devices receive security scrutiny while leaving others potentially vulnerable.
Alongside, device diversity and resource constraints, physical access requirements also create logistical challenges. Unlike web applications tested remotely, embedded device testing demands physical possession of hardware. Organizations with geographically distributed deployments face difficulties collecting representative samples and managing inventory. Destructive testing techniques mean tested devices cannot return to production, creating additional procurement costs.
Limited documentation and proprietary systems further complicate assessment in embedded devices. Manufacturers often obscure implementation details to protect intellectual property, forcing penetration testers to spend significant effort reverse engineering basic functionality before security testing begins. Third-party components and outsourced firmware development mean organizations may lack complete visibility into their own products’ internal workings.
Modern firmware often incorporates multiple layers of protection. While these protections enhance security against attackers, they require testers to apply additional expertise to analyse protected binaries.
Additionally, custom toolchains, proprietary compilers, and non-standard file systems further complicate firmware analysis. Unlike mainstream software built with standard development tools, embedded firmware may use specialized build processes that produce binaries enquiring familiarity with the specific instruction set architecture and memory layout. As long as the instruction set architecture and memory layout are known, the binary can be reverse‑engineered, the toolchain itself does not prevent analysis.
Best Practices for Embedded Penetration Testing
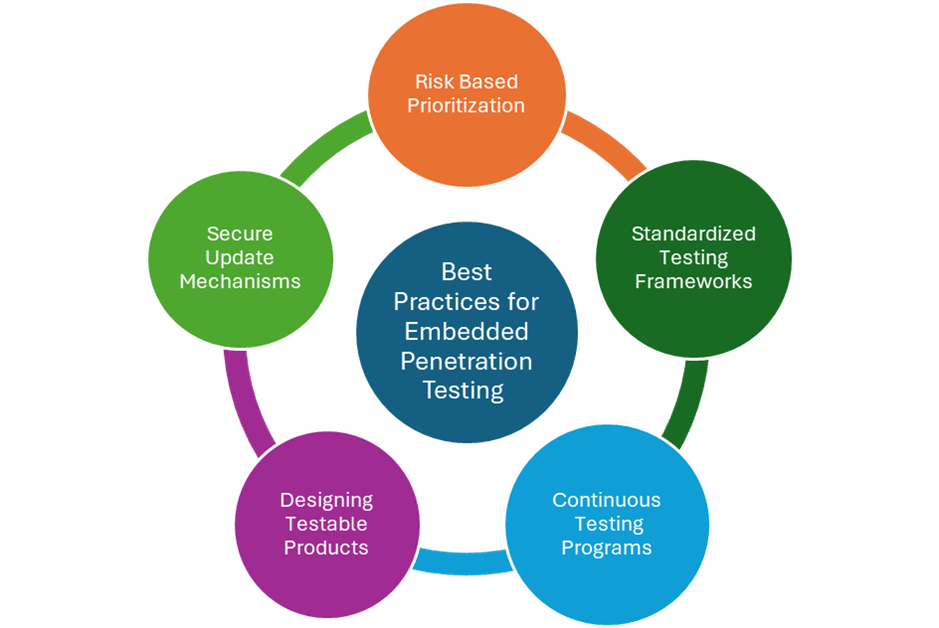
Organizations can address the above challenges through strategic approaches that balance thoroughness with practical constraints.
- Implementing risk-based prioritization: Organizations should focus testing resources on devices with the highest potential impact by evaluating internet exposure, data sensitivity, deployment scale, attack surface and potential impact of compromise.
- Establishing standardized testing frameworks: While every embedded products have unique characteristics, common testing tasks, firmware extraction, JTAG enumeration, protocol analysis, can be standardized into repeatable procedures. Documented methodologies for these building blocks enable consistent coverage even across heterogeneous device families, reducing reliance on individual expertise and improving comparability of results.
- Adopting Continuous Testing Programs: Integrating security testing throughout the product lifecycle will help identifying vulnerabilities early when remediation is simpler.
- Designing Products for Testability: Incorporating debug interfaces that can be disabled in production, implement modular architectures, and provide comprehensive documentation will help accelerating security assessment.
- Establishing Secure Update Mechanisms: Penetration testing is only valuable when discovered vulnerabilities can be fixed. Secure update mechanisms including cryptographic verification of firmware updates, fail‑safe rollback capabilities, and automated delivery systems are therefore a prerequisite for making remediation actionable. Without them, even a thorough pentest cannot translate into improved device security.
Conclusion
As embedded systems become increasingly critical to industrial, healthcare, and consumer infrastructure, security testing will transition from compliance requirement to fundamental operational necessity.
Keeping a note of this its is essential for organizations to integrate security into development pipelines and embedded penetration testing will be a cornerstone in this effort. It will provide organizations with empirical evidence to understand their true attack surface, prioritize remediation, and demonstrate due diligence to regulators and customers alike.