An automotive IDS, or Intrusion Detection System, is a secure mechanism designed to continuously monitor vehicle network traffic to detect malicious activities and cyber intrusions.
Before the introduction of ISO/SAE 21434, automotive cybersecurity lacked a unified definition. Every OEM and supplier had their own isolated approach to security. And most of them only focused on pre‑deployment attack prevention.
However, this was not at all sufficient!
On-road vehicles today interact with various external interfaces and communication channels (i.e. telematics, V2X, mobile apps, cloud). While these endpoints enable the smart features, they simultaneously open a portal of cyber-attacks that attackers use to target in running cars.
ISO 21434 standard addressed this gap in its Clause 13. Alongside security controls integration, manufacturers are also responsible for an efficient post-production incident response and management. This is exactly where automotive IDS come in. It detects, logs and reports any abnormal behaviour in vehicle network patterns when a vehicle interacts with external endpoints.
This article will dive deeper to help you understand the implementation of IDS in modern vehicles. Further, we will also break down how they operate and function within AUTOSAR based architectures.
What Is an Automotive Intrusion Detection System (IDS)?
An automotive intrusion detection system (IDS) is like enterprise IT security tool but built for vehicles. It monitors in-vehicle networks, ECUs, and system behaviour to detect cyber threats, while working within the constraints of automotive systems.
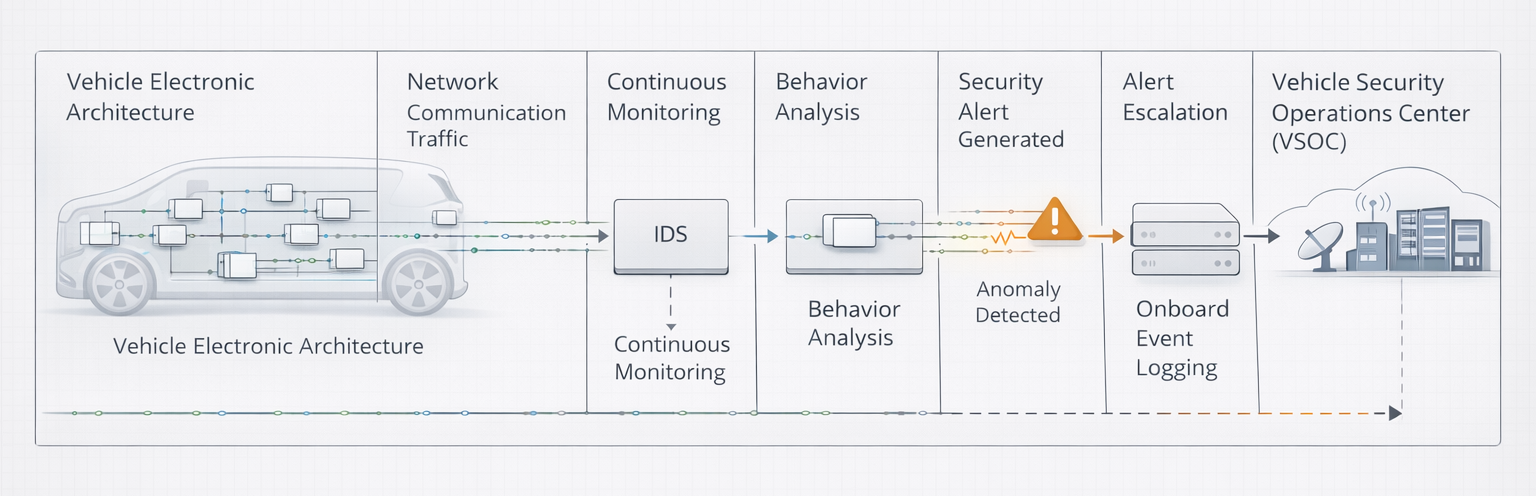
At its core, the system continuously monitors all traffic flowing across a vehicle’s electronic architecture, including CAN bus, LIN, automotive Ethernet, Bluetooth, Wi-Fi, and telematics interfaces. It analyses the behaviour of messages exchanged between Electronic Control Units (ECUs) and flags anomalies or recognized attack patterns as they occur.
When a suspicious activity is detected, the system generates a security alert that is logged onboard and escalated to a vehicle Security Operations Centre (vSOC) for investigation and response.
Operational Approaches in Automotive IDS
Anomaly detection in post-production deployments is only half the picture. For functional operations, the solutions typically rely on two complementary detection approaches.
Signature-based detection uses a pre-built library of known attack patterns. It compares observed network activity against an attack library. When a CAN frame, Ethernet packet, or system event matches a catalogued threat signature, the IDS raises an alert.
On the other hand, anomaly-based detection operates using a behavioural approach. Rather than matching against a fixed library, it establishes a baseline model of normal vehicle network activity, including typical message frequencies, inter-message timing intervals, ECU communication patterns, and expected payload value ranges. During operation, it continuously monitors for statistical deviations from that baseline and flags them as potential intrusions.
Nevertheless, neither approach is sufficient in isolation. While signature-based detection handles known threats, anomaly-based detection extends coverage to the unknown. Most production-grade automotive IDS architectures are designed to support both methods to run in parallel. Each trigger generates security events that feed into the same centralised management and reporting pipeline.
Types of Automotive IDS
Now, that we know the threat detection mechanism it is evident, how threats are identified. However, this is only half the equation; the efficiency of the detection system functions efficient only when deployed in the right architecture.
In practice, IDS implementations are typically deployed at two distinct levels:
- Network-Based IDS (NIDS) and
- Host-Based IDS (HIDS).
Each addresses a different attack surface, and both must operate in tandem for end-to-end coverage.
| Attribute | Network IDS (NIDS) | Host IDS (HIDS) |
| Deployment location | Central gateway ECU / Domain Controllers | Individual ECUs |
| What it monitors | Inter-ECU network traffic | System calls, processes, file integrity |
| Attack types detected | Injection, spoofing, DoS, replay, fuzzing | Privilege escalation, malware, rootkits |
| Resource requirements | Moderate (centralised) | Higher (per-ECU overhead) |
As is clear from the table above, Network IDS (NIDS) is designed to monitor traffic traversing the in-vehicle communication. It observes message exchanges across networks such as CAN, CAN FD, LIN, and Automotive Ethernet, analysing traffic patterns in real time to detect anomalies or known attack signatures.
While Host IDS (HIDS) operate directly on individual ECUs, particularly for those running on rich operating systems like Linux, Android, or QNX. Rather than monitoring network packets, it examines system calls, process behaviour, file integrity, and runtime memory to detect compromise from within.
Why do Vehicles require both NIDS and HIDS? How do they operate?
From a security engineering standpoint, both deployment models are necessary in vehicles to ensure a “T” shaped threat visibility.
Both models operate in tandem. Network-Based IDS provides horizontal visibility across communication channels but cannot see inside an ECU’s operating environment. And Host-Based IDS delivers vertical visibility with deep ECU-level forensics but cannot access the bus-level traffic patterns.
Relying on only one approach creates blind spots.
In a production-grade deployment, security events from both models are fed into the same pipeline where the threats are aggregated, filtered, and escalated to a centralized vSOC for a unified threat picture. However, the architecture behind this pipeline is not simple; it comes along with numerous operational complexities.
How Automotive IDS Works: The AUTOSAR Architecture
Automotive Intrusion Detection Systems are mostly built on the AUTOSAR framework. This is not because standards like ISO/SAE 21434 or UNECE R155 require it, but because AUTOSAR gives OEMs and suppliers a well-structured foundation to work from.
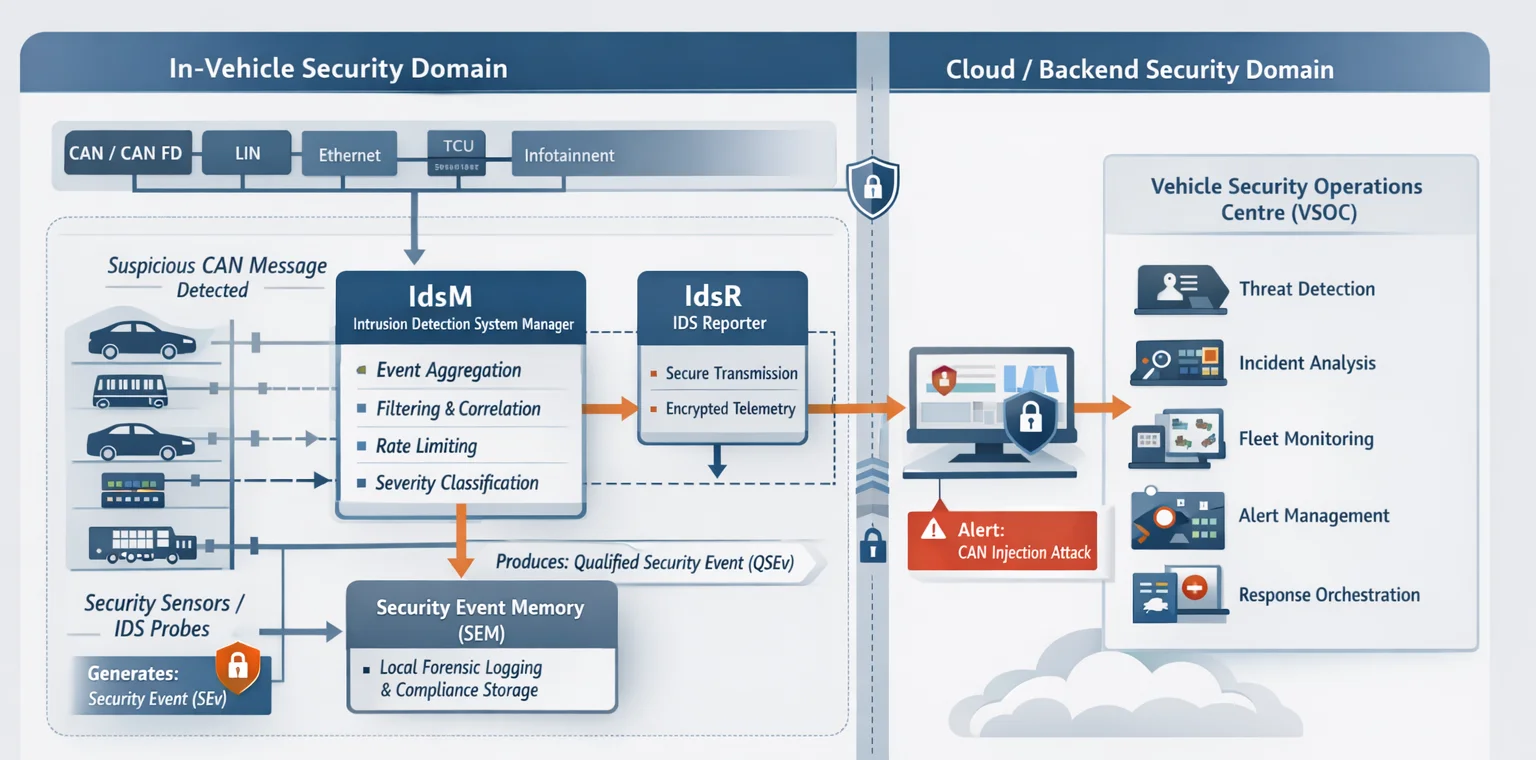
It provides standardized software module definitions that make IDS components portable and consistent across different ECU platforms. Within the AUTOSAR framework, a set of dedicated modules work together to move security events from the moment they are detected all the way through to the team responsible for acting on them. In a typical deployment, this journey passes through five functional stages, each with a specific role in filtering, storing, and reporting threat data before it reaches the vSOC.
| Security Sensors | Also known as security probes, these are software algorithms embedded on individual ECUs that continuously monitor CAN frames, Ethernet packets, and system behaviour.
Whan a suspicious activity i.e., an anomalous message frequency, unexpected payload value, out-of-sequence frame is identified, the sensor generates a structured alert called Security Event (SEv) with event identifier, timestamp, source ECU address, network interface or process context and detected anomaly or signature match. |
| IdsM (IDS Manager) | The IdsM collects security events from sensors and acts as the decision layer. Instead of forwarding everything, it filters out duplicates, limits excessive events, and combines related signals to create meaningful alerts called Qualified Security Events (QSEv).
This filtering acts as a critical step, in its absence a single DoS attack generating thousands of frames per second can overwhelm the reporting pipeline. |
| SEM (Security Event Memory) | Once events are qualified, they are stored within the Security Event Memory (SEM).
It serves as the vehicle’s onboard forensic repository that provides an immediate forensic trace for post-incident analysis and ensures no event data is lost if the telematics channel is temporarily unavailable. |
| IdsR (IDS Reporter) | Post local processing and storage of Security Events the incident data is securely transmitted to external monitoring infrastructure.
The IdsR manages this. It establishes a secure communication channel between the vehicle and backend systems, typically using encrypted telematics connectivity and ensures that Qualified Security Events are reliably transmitted without being intercepted or manipulated. |
| vSOC (Vehicle Security Operations Centre) | The vSOC acts as the central command hub responsible for monitoring cybersecurity risks.
Upon receiving qualified, filtered event data they investigate anomalies, determine threat severity, and if necessary, trigger OTA counter measures or escalate to an incident response team. |
How is Automotive IDS Tested?
A well-designed IDS improves threat detection, but its effectiveness depends on validation under controlled conditions. Before production, AUTOSAR-based IDS components must be tested at system level to ensure correct detection, filtering, and reporting under simulated attack scenarios.
This is typically done via a deliberate rule violation where malicious or abnormal network traffic is intentionally injected to trigger IDS rules. These tests validate detection accuracy, event handling within IdsM, and end-to-end reporting to backend systems.
Once a rule is violated, the IDS generates an incident. This incident data is captured in real time and monitored using ESO Trace Viewer that gives live visibility into what the IDS is reporting as events propagate through the pipeline.
The raw incident data is simultaneously captured in Pocket Capture (PCAP) files. This output is then decoded with a decoder tool for human interpretation.
The raw incident data is simultaneously captured in Pocket Capture (PCAP) files. This output is then decoded with a decoder tool for human interpretation.
The objective of this validation process is precisely to confirm-
- Which rule was triggered
- Verify that the rule details match the simulated violation
This establishes that the detection pipeline produced the expected qualified event output.
Once an automotive IDS is validated, it can be deployed for continuous surveillance. However, detection alone does not neutralise a threat, it requires a secure mechanism for prevention. And this leads us to the often-asked question in the next section.
Does IDS also Prevent Cyberattack?
An IDS is fundamentally designed as a surveillance and detection layer, not an enforcement mechanism. Its primary responsibility is to continuously monitor vehicle network activity, analyse behavioural patterns, and generate alerts whenever suspicious activity is identified.
In other words, the presence of an IDS does not alter the behaviour of the vehicle network in real time. The system observes and reports, but it does not block, throttle, or terminate malicious traffic. The vehicle continues to operate as it would have without the IDS in place, while the incident is logged and escalated for analysis.
So, the question here is if IDS do not prevent attacks, then what happens next?
How are Automotive Attacks Prevented Post Detection?
It’s no new fact that only detection can neutralise a threat. Once the IDS flags an anomaly and escalates it to the vSOC, the vehicle still needs a mechanism that can actively intervene. It requires a mechanism that goes beyond observing and acts on the intelligence gathered.
An Intrusion Prevention System (IPS) plays the same role when it comes to prevention post detection.
What is Intrusion Prevention System (IPS)? How is it Different from IDS?
An Intrusion Prevention System (IPS) is a security control designed to automatically respond to detected threats by actively intervening in network communication.
Unlike an IDS, which operates in a monitoring role, an IPS functions as an inline enforcement mechanism positioned directly within the data path of the vehicle network. When suspicious activity is detected, the IPS can take immediate action based on predefined security policies and can block, quarantine, or throttle traffic autonomously.
| Attribute | IDS | IPS |
| Primary function | Detect and alert | Detect and respond |
| Deployment position | Out-of-band monitoring | Inline on network gateway |
| False positive risk | Alert noise | Potential safety violation |
| Latency requirement | Low | Critical, must not delay safety messages |
Why Is IPS Not Used Instead of IDS?
With the clear difference just referenced above it is quite evident that IPS is much more beneficial than IDS, therefore the obvious question is why IDS is still in use.
Well, most IPS documentation misses a critical automotive constraint: an IPS must not interrupt safety‑critical traffic. Braking, steering, and powertrain messages operate under strict deterministic timing. Any inline control that adds latency or drops frames on these paths, even in response to a legitimate attack, can trigger a functional safety failure.
Because of these risks, automotive IPS solutions either need very careful engineering or adopt a phased strategy solution called Intrusion Detection Prevention System (IDPS).
What is IDPS?
Intrusion Detection and Prevention System (IDPS) is a combined solution that integrates both capabilities of both IDS and IPS.
This solution deploys IDS to establish baseline threat visibility to analyse attack patterns and system behaviour. Additionally, it selectively enables IPS-grade enforcement only on channels where safety analysis confirms it is permissible.
Conclusion
- UN R155 made post-production cybersecurity monitoring a legal obligation across 64+ countries in July 2024.
- ISO 21434 Clause 13 defines the operational framework.
- GB 44495:2024 since introduction has additional IDS verification requirements for global programmes.
As software-defined architectures expand vehicle attack surfaces, regulatory bodies will continue to demand deeper IDS verification with broader protocol coverage, AI-augmented detection capabilities, and tighter VSOC integration. This preparation for a future ready and scalable security solutions needs the right plan of action today to absorb regulatory requirements without starting over.
We at Embitel are focused on developing and validating the right security solutions for next-gen vehicles. Learn more about our Automotive Cybersecurity services.


