V2X or Vehicle-to-Everything security refers to the controls implemented to protect the wireless communications that connects vehicles to external surroundings from cyber threats and vulnerabilities.
Over the past few decades, connectivity has moved beyond IoT. It now sits inside the machines we use every day. Systems that were once purely mechanical are shaped by software, enabling capabilities they were never originally built for.
The automotive stack is no exception to it. A vehicle today boasts features that not only make it move but also connects it to external ecosystems enabling functionalities like:
- Communication with another vehicle.
- Broadcast safety alerts to roadside infrastructure in real time.
- Receive network-level updates and traffic data from centralised systems.
This connectivity is made possible by Vehicle-to-Everything communication protocols that allow vehicles to share live data across an entire ecosystem. However, this growth is driven as much by risk as by opportunity. Every message a vehicle broadcasts can be spoofed, jammed, or replayed, with consequences ranging from traffic disruption to safety-critical incidents.
This guide breaks down what V2X security is, the threats that make it critical, the standards that govern it, and the mitigating strategies.
What Is V2X Security? What Makes it Critical?
V2X, or Vehicle-to-Everything, is a broad communication framework that connects vehicles to every element of the transport ecosystem around them. And V2X security is the set of protocols, technologies, and standards put in place to protect those wireless communications against cyberattacks, data tampering, and unauthorised access.
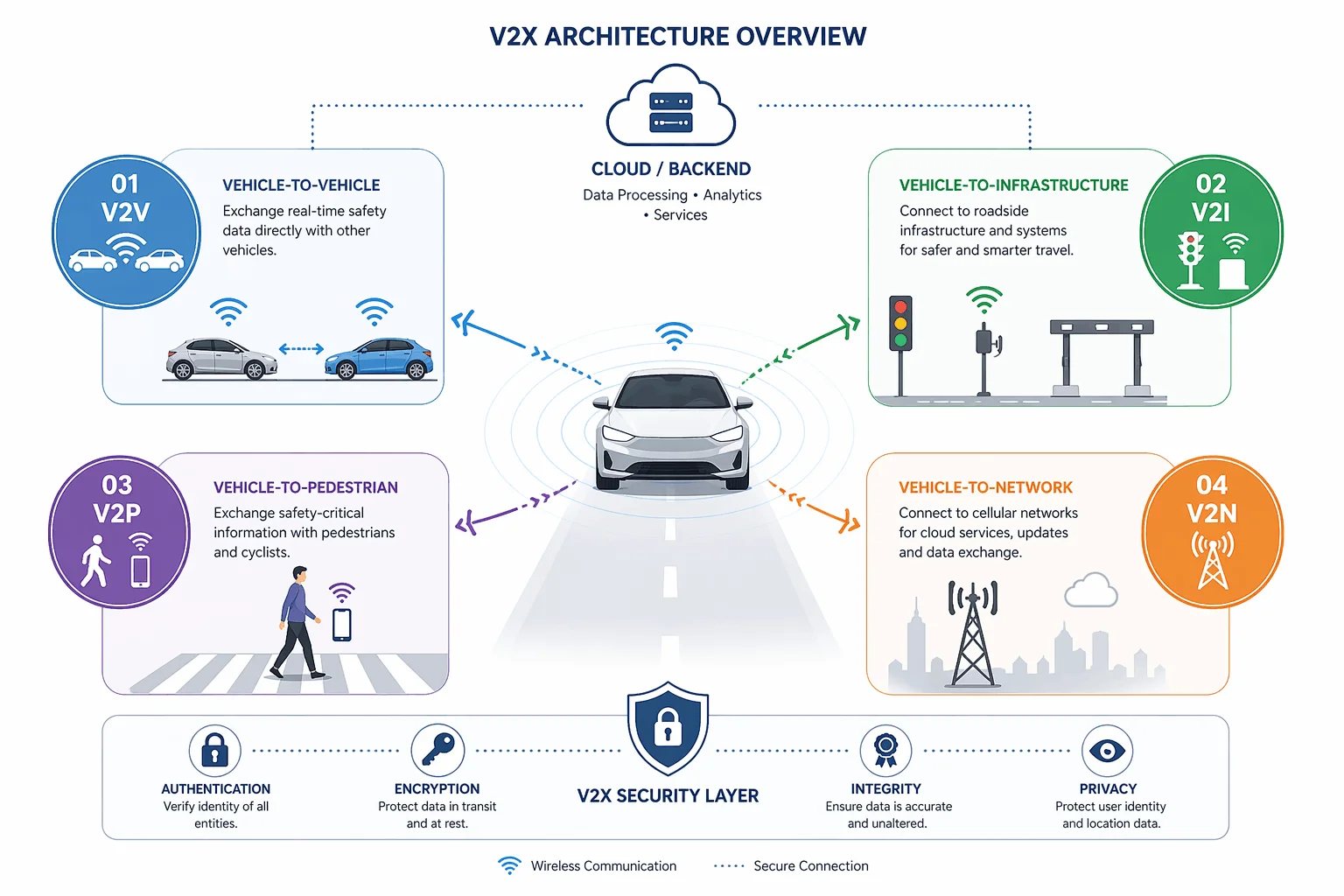
This communication framework generally spans 4 distinct interaction types, each with its own function and exposure.
- Vehicle-to-Vehicle (V2V) that enables vehicles to exchange real-time safety data, including sudden braking events, lane changes, and collision warnings, directly with one another.
- Vehicle-to-Infrastructure (V2I) that connects vehicles to roadside infrastructure, including traffic signal controllers, toll systems, and roadside units.
- Vehicle-to-Pedestrian (V2P) that facilitates safety-critical exchanges with pedestrians and cyclists equipped with connected devices.
- Vehicle to Network (V2N) that links the vehicle to cellular networks for dynamic traffic management, remote diagnostics, and OTA updates.
Each of these channels carries a different risk profile and securing one does not automatically secure the others. For example, a compromised V2I channel can manipulate traffic signal timing without ever touching the V2V layer and vice versa. Similarly, a spoofed V2P alert can trigger unnecessary emergency braking in vehicles that have no direct visibility of the pedestrian.
But the deeper concern is not just what these protocols exchange, it is what they authorise. In an increasingly automated ecosystem, V2X messages do not just inform the vehicles, they instruct. And in such scenario, any falsified manipulation i.e., emergency braking signal, a replayed intersection clearance, or an injected speed advisory can translate directly into physical action on the road.
Moreover, the degree of exposure is shaped directly by the wireless technology the network runs on. Which brings us to the next question: What runs behind V2X communication?
The Technology Behind the V2X Communication
V2X communication runs on one of two underlying wireless technologies, and each has a distinct security architecture and deployment history.
- Dedicated Short-Range Communications (DSRC)
- Cellular Vehicle-to-Everything (C-V2X)
Dedicated Short-Range Communications (DSRC)
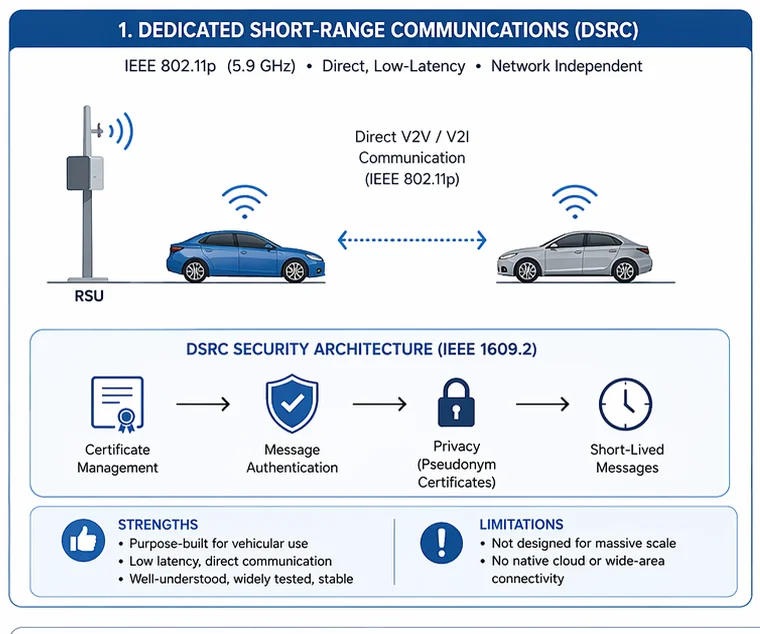
Built on the IEEE 802.11p standard and operating in the 5.9 GHz spectrum, DSRC is purpose-built for vehicular communication. It supports direct, low-latency message exchange between vehicles and roadside units without relying on a cellular network.
Its security framework is defined under IEEE 1609.2 standard, which governs certificate formats, message authentication, and privacy protections. DSRC’s maturity is both its strength and its limitation, the standard is well-understood, widely tested, and stable, but its architecture was not designed with the scale of today’s connected vehicle deployments in mind.
Cellular Vehicle-to-Everything (C-V2X)
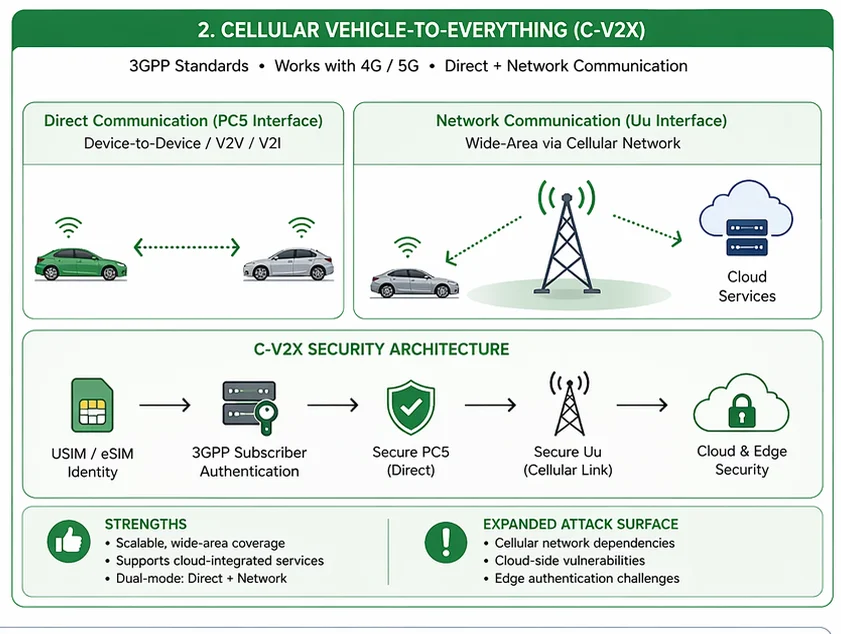
In contrast to DSRC, C-V2X is built on 3GPP standards and increasingly paired with 5G networks. It supports both direct device-to-device communication (via the PC5 interface) and wide-area network communication through cellular infrastructure (via the Uu interface).
This dual-mode capability gives C-V2X a significantly broader reach and opens the door to cloud-integrated safety applications that DSRC cannot support. However, it also expands the attack surface, introducing cellular network dependencies, cloud-side vulnerabilities, and edge authentication challenges that do not exist in a DSRC-only deployment.
Regardless of the technology underpinned in a V2X deployment by OEM or supplier, the threat landscape it faces is consistent. The attack vectors change in scale and complexity depending on whether the network runs on DSRC or C-V2X, but the categories of risk remain the same. Understanding them is the first step to knowing what a security solution needs to defend against.
Threat Landscape in V2X Networks and Applicable Standards
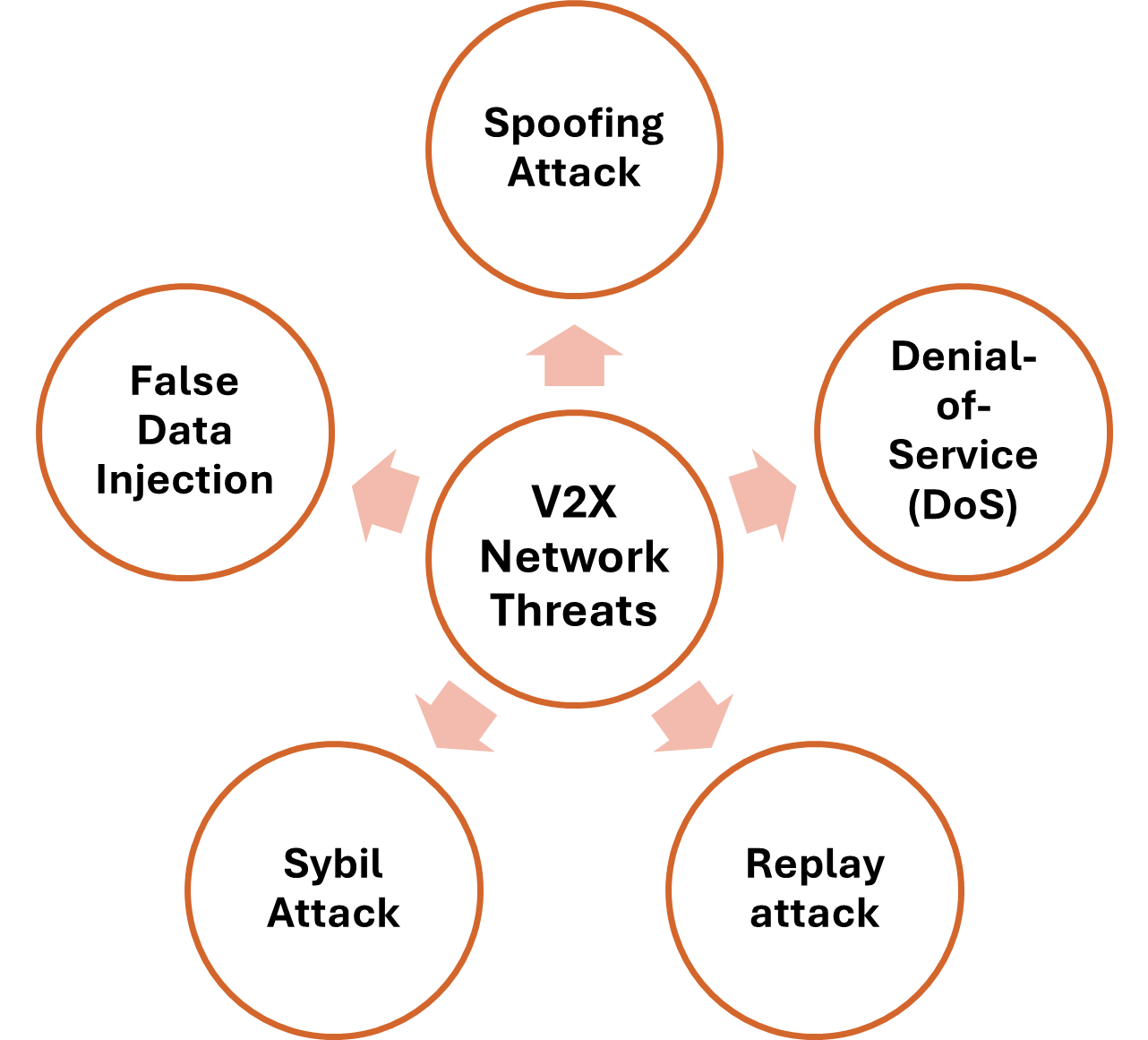
Unlike traditional IT environment where threats are largely contained to data, V2X threats have a direct physical dimension. However, the V2X networks are exposed to specific and well-documented set of cyberattacks categorized under five categories.
In the table below, we have classified these threats and what regulatory bodies require for their security.
| Threat | What Happens | Regulatory Obligations |
| Spoofing Attack | A malicious actor impersonates a legitimate vehicle, On-Board Unit (OBU), or Road-Side Unit (RSU) and injects false messages into the network. It fabricates emergency braking events, ghost vehicles, or hazard alerts that nearby vehicles act on in real time. | IEEE 1609.2 mandates cryptographic message signing and certificate-based identity verification for all V2X participants. UNECE WP.29 R155 requires OEMs to demonstrate threat identification and risk treatment for impersonation attacks within their Cybersecurity Management System (CSMS). |
| Denial-of-Service (DoS) / Channel Jamming | An attacker floods the V2X channel with illegitimate traffic or physically disrupts the 5.9 GHz / cellular spectrum, preventing legitimate safety messages from reaching their destination. This deprives nearby vehicles of the real-time situational awareness they depend on to make safe driving decisions. | ISO/SAE 21434 treats message availability (the guarantee that safety-critical communications to remain accessible and timely) as a cybersecurity parameter. This means any threat to V2X service continuity must be pre-assessed in a TARA and assigned a cybersecurity goal with corresponding controls. Further, UN R155 mandates incident detection and response capabilities to remain operational across the vehicle’s entire lifecycle. |
| Replay Attack | In a replay attack, a valid V2X message, such as a genuine emergency alert or intersection clearance signal, is captured and retransmitted at a later time or from a different location. The message passes authentication checks because it was originally signed by a legitimate source, but it describes conditions that no longer exist, causing vehicles to act on false context. | IEEE 1609.2 defines certificate validity windows and timestamp requirements to limit the reuse window of captured messages. ISO/SAE 21434 TARA must account for replay as a distinct attack path with its own risk rating and treatment. |
| Sybil Attack | A single attacker generates multiple fake identities and broadcasts simultaneously from all of them, fabricating traffic events, simulating multi-vehicle incidents, or corrupting the misbehaviour detection systems that rely on network consensus to identify anomalous nodes. | UN R155 requires misbehaviour detection mechanisms to be part of the CSMS. The EU CCMS Certificate and Misbehaviour Management System (CCMS) specifically include a Misbehaviour Authority to identify and revoke certificates associated with anomalous behaviour patterns. |
| False Data Injection | A compromised vehicle manipulates its own telemetry, speed, location, heading, before broadcasting. Because the message originates from a legitimate, credentialled node, it passes standard authentication checks. Surrounding vehicles receive cryptographically valid but factually incorrect data. | ISO/SAE 21434 requires security controls to extend to the integrity of data at the point of generation, not just in transit. UNECE WP.29 R155 mandates that OEMs assess the risk of compromised in-vehicle components contributing falsified data to external networks as part of their CSMS scope. |
How is V2X Communication Security Ensured?
V2X security is not a single control, it is a layered system. And understanding the threats and the regulations that govern it only answers the what and the why.
To fulfil regulatory requirements, OEMs and suppliers rely on security engineering solutions that effectively mitigate the risks.
Public Key Infrastructure (PKI)
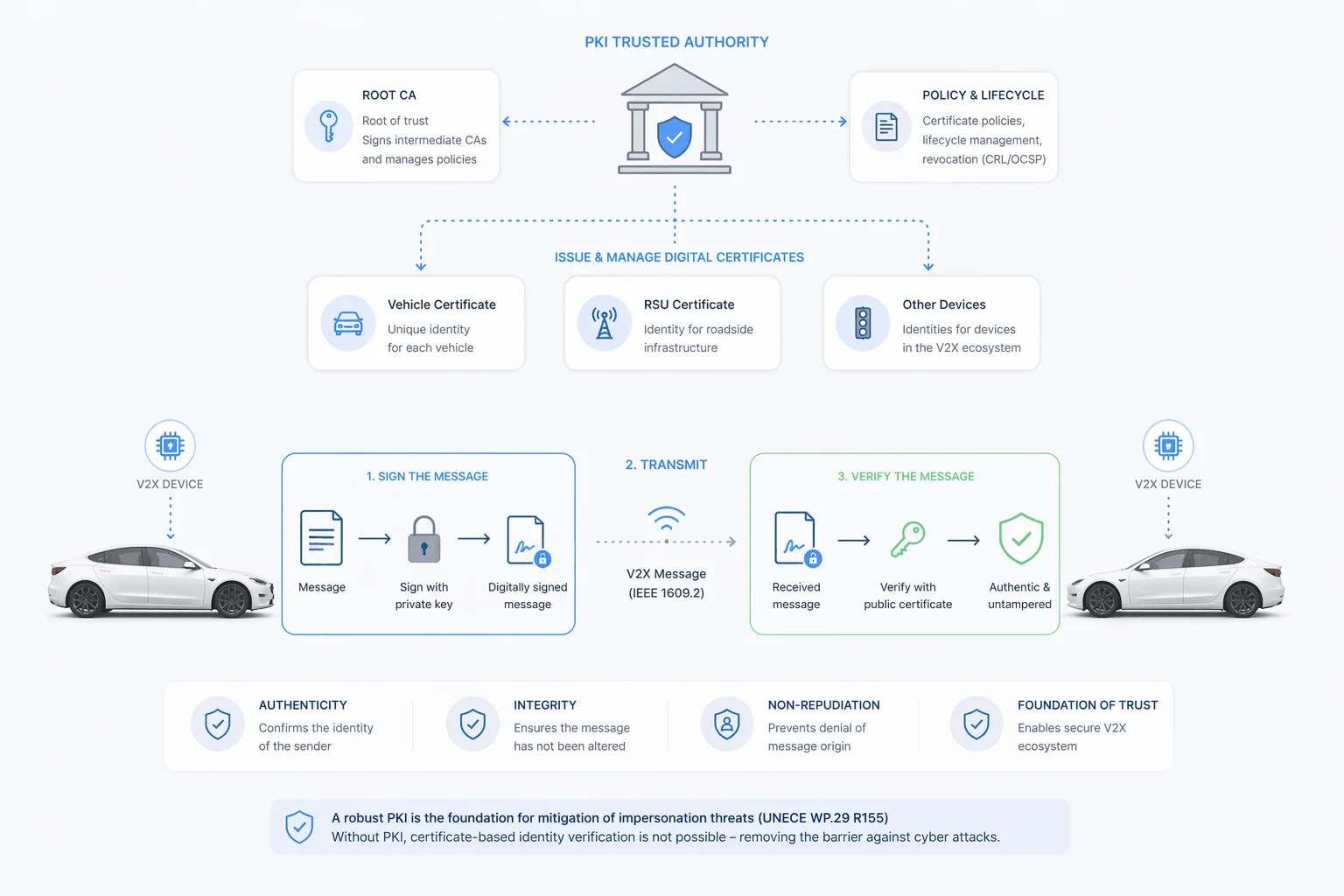
At the core of V2X security deployment is the Public Key Infrastructure (PKI). It is the system that establishes and verifies the identity of every participant in a V2X network.
In practice, every V2X device is issued a digital certificate by a trusted authority. When a vehicle broadcasts a message, that message is cryptographically signed using the device’s private key. Any receiving unit can verify the signature against the corresponding public certificate to confirm that the message is authentic and has not been tampered with in transit.
This is the technical mechanism that IEEE 1609.2 mandates. It is also the foundation on which UNECE WP.29 R155’s requirement for impersonation threat treatment is built. Without a functioning PKI, certificate-based identity verification is not at all possible and its absence can remove technical barrier which may lead to cyber-attacks.
Learn more about PKI and our PKI offerings.
Credential Management
While PKI defines how trust works in the Security Credential Management System (SCMS), Certificate Credential Management System (CCMS) defines how it is administered.
These generally operate as the backend systems responsible for the full lifecycle of every certificate in the network. In practice, when a vehicle is manufactured, it’s on-board unit (OBU) is enrolled in the relevant credential management system and issued a set of operational certificates. As those certificates expire, the SCMS issues new ones. When a device is compromised or behaves anomalously, the SCMS revokes its certificates and removes it from the trusted network.
This is how CCMS’s Misbehaviour Authority directly addresses the Sybil attack obligation. Misbehaviour reports from vehicles in the field are aggregated and analysed. When suspicious patterns are detected, the Authority revokes the pseudonym certificates of the flagged nodes, even without identifying the underlying vehicle.
Pseudonym Certificates
While PKI solves the message authentication challenge, there are a few roadblocks along the way. If a vehicle continuously transmits the same certificate, it can be monitored, its movement is logged, and its driver profiled. Although, this ensures communication network safety, it breaches the GDPR privacy compliance.
Moreover, it becomes even more critical as ISO/SAE 21434 treats privacy as a cybersecurity property.
To tackle this, Pseudonym certificates are used by OEMs and suppliers. These are temporary digital certificates used to authenticate message. Rather than broadcasting a permanent identity, these certificates are used that at regular intervals. To an outside observer, the vehicle appears as a different entity after each rotation. This preserves the authentication with every message, simultaneously ensuring the privacy is safeguarded.
Hardware Security Modules (HSMs)
Every security mechanism described above depends on one assumption: that the private keys used to sign V2X messages have not been compromised.
If an attacker gains access to a vehicle’s signing key, every message it broadcasts will be cryptographically valid, regardless of its content. This can result in false data injection scenario which is one of the hardest threats to detect after the fact.
To mitigate this, ISO/SAE 21434 requires security controls to extend to the integrity of data at the point of generation. Hardware Security Module or HSM plays the same role. It is a dedicated, tamper-resistant chip embedded in the OBU or RSU that stores private keys in isolation from the rest of the vehicle’s electronic systems.
The HSM does not expose the key and performs the signing operation internally and returns only the signature. It is designed in way where even if a vehicle’s operating system gets fully compromised an adversary cannot extract the key or sign arbitrary content without the HSM’s controlled execution environment.
OTA Updates

UN R155 does not treat cybersecurity as a point-in-time certification. It requires OEMs to continuously monitor, detect, and respond to threats across the entire operational life of a vehicle. In practice, this means the security configuration of every OBU and RSU in a deployed network must be updatable after the vehicle leaves production.
Secure Over-the-air (OTA) update fulfils the post-production security requirements of OEMs. It allows certificate stores to be refreshed, security parameters to be adjusted, and newly identified vulnerabilities to be patched without recalling vehicles or requiring physical access to roadside units. This mechanism cryptographically verifies updates only from OEMs as manipulated OTA updates can install malicious files which can entirely corrupt the security of vehicles.
To understand more about how OTA is secured read our article on: OTA Updates Security: What Makes it Actually Secure?
Wrapping up
V2X security is not a standalone discipline, it is the outer boundary of a much larger challenge. The solution architecture covered in this article: PKI, credential management, pseudonym certificates, HSMs, and OTA, does not operate in isolation, each of these layers depends on the others, and a gap in any one of them is a gap in all of them.
Moreover, as V2X deployments scale and regulatory obligations tighten, the organisations that get ahead are those that treat security as an engineering decision made during initial development. The threat categories are documented. The standards are binding. The architecture is understood.
What remains is implementation, and that is where the specifics of your stack, your deployment model, and your market obligations determine what that looks like in practice.
If you are working through any of these layers our automotive cybersecurity practice covers the full development stack, checkout now.